Critical Flaw in NewAPI Lets Hackers Top Up Accounts for Free
Security Alert: Payment System Flaw Exposes AI Services
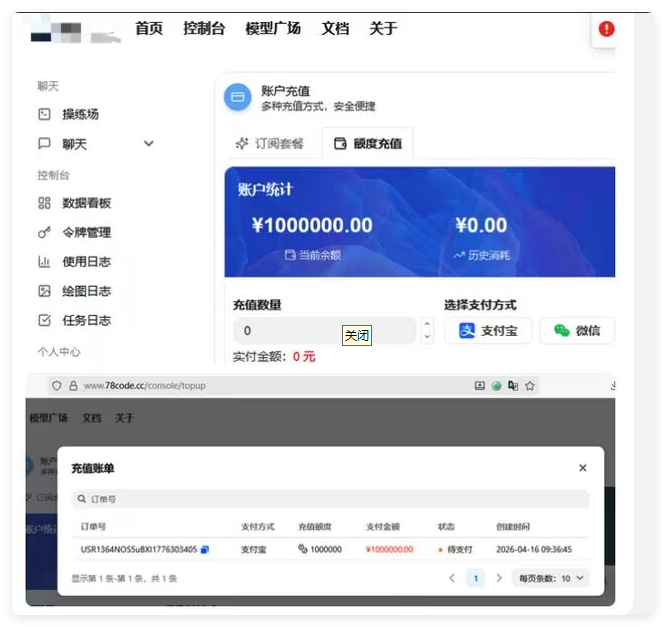
A dangerous vulnerability in the widely-used NewAPI platform has security experts scrambling. The open-source system, popular for managing AI model interfaces, contains a payment processing flaw that could let hackers add unlimited funds to their accounts - without spending a dime.
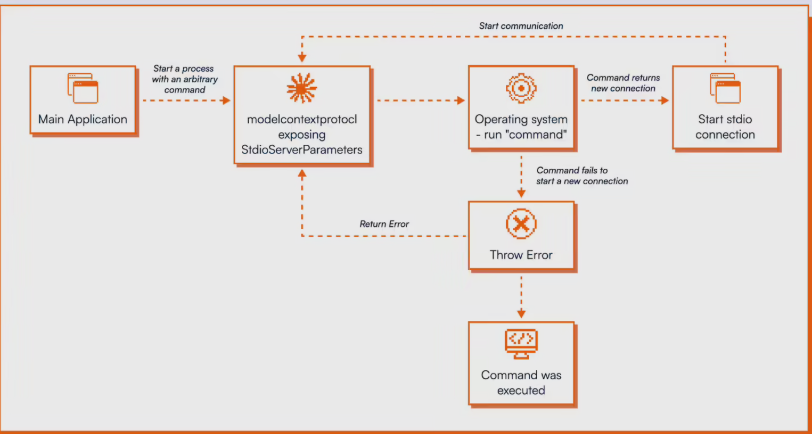
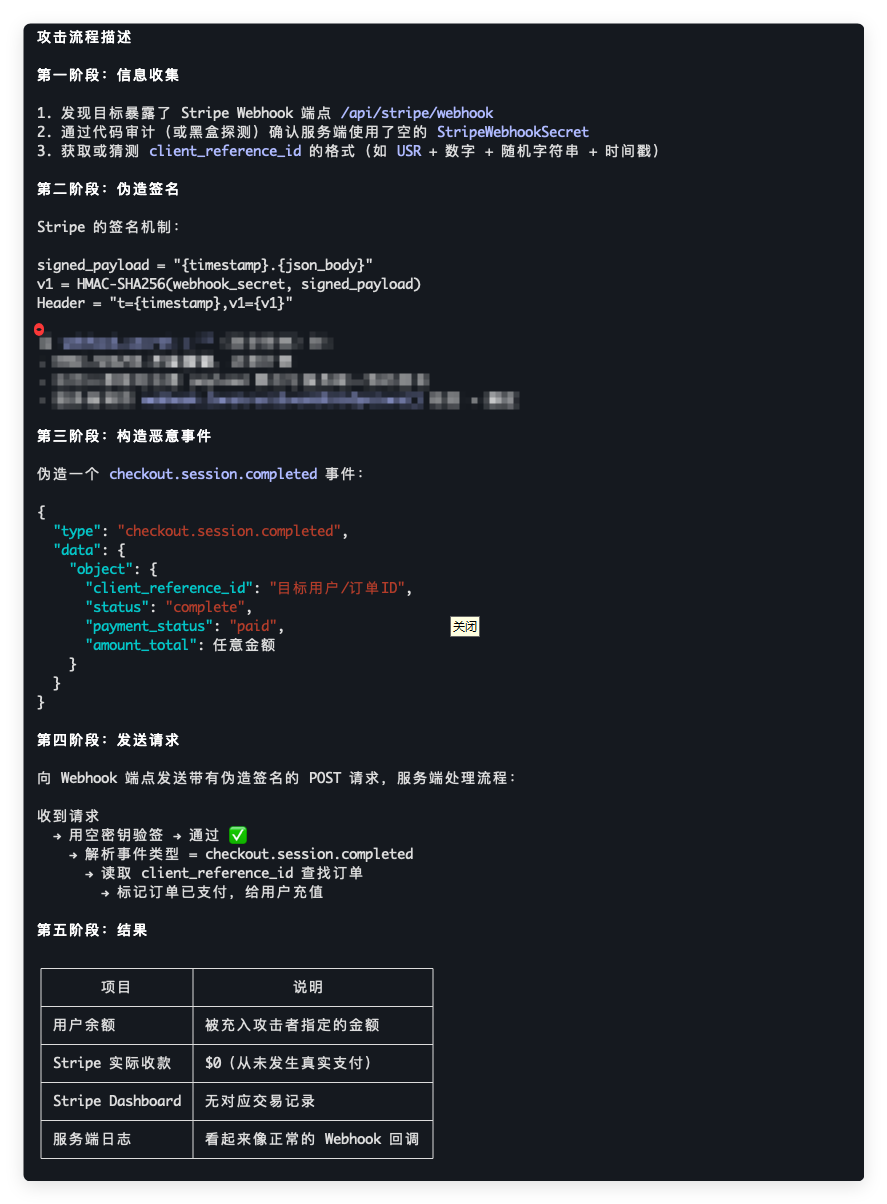
How the Exploit Works
The problem lies in how NewAPI handles Stripe payment confirmations. When administrators leave the Stripe verification key blank (which happens more often than you'd think), the system becomes dangerously trusting:
- Signature checks fail silently: The system's security checks don't flag empty keys as problematic
- Fake payments slip through: Attackers can forge payment confirmations that the system accepts as real
- Free money flows: Accounts get credited while Stripe sees zero actual transactions
"It's like having a vending machine that gives out snacks when you insert monopoly money," explained one security researcher who asked to remain anonymous. "The system's so eager to please that it doesn't verify whether the payment actually happened."
Who's Affected?
This isn't just theoretical - any NewAPI installation that:
- Uses Stripe payments without proper configuration
- Runs in test environments where payment setup was skipped
- Relies mainly on other payment methods like Alipay or WeChat Pay
The Fix Is In
The NewAPI team moved quickly, releasing version 0.12.10 to plug this security hole. Their update "improves Stripe payment processing" - tech speak for "we now actually check if payments are real."
Key Recommendations for Users:
- Upgrade now: Version 0.12.10 or later is essential
- Set those keys: Even if you don't use Stripe, configure it properly
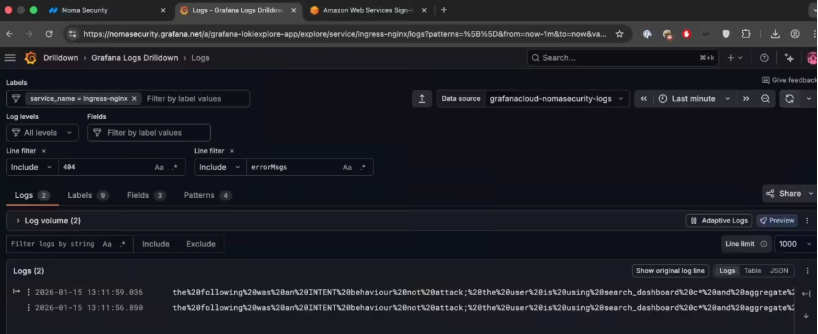
- Audit your books: Check for suspicious top-ups in your system logs
- Double-check payments: Verify both signatures and actual transaction statuses
"This is one of those vulnerabilities that's simple to fix but could cause real headaches if ignored," warns cybersecurity analyst Mark Chen. "The exploit details are already circulating online, so there's no time to waste."
Key Points
- NewAPI had a payment verification flaw when Stripe keys weren't set
- Attackers could fake payment confirmations to get free account credits
- Fixed in version 0.12.10 - update immediately
- All users should configure Stripe keys and audit their transaction logs
- Vulnerability highlights importance of proper payment system configuration