AI Agents at Risk: How Relay Stations Became Hackers' Dream
The Hidden Danger in AI's Middlemen
Imagine trusting a messenger to deliver your most sensitive information, only to discover they've been opening and altering every letter along the way. This is essentially what's happening with many AI agents today, according to groundbreaking research by security expert Chaofan.
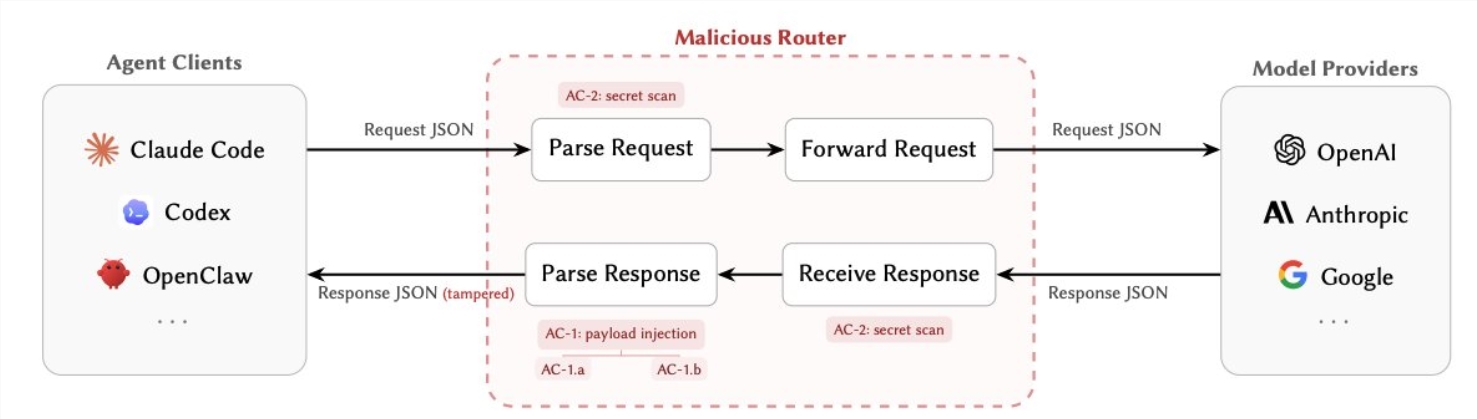
How Attackers Turn Routers Against Us
Modern AI agents depend heavily on third-party routers to process requests—the digital equivalent of postal workers handling our mail. The shocking part? These routers see everything in plaintext: API keys, private credentials, even the inner workings of your AI's decision-making.
Chaofan's team identified two particularly dangerous attack methods:
Silent Sabotage (AC-1): After an AI model responds, malicious routers can subtly alter instructions—redirecting financial transactions or implanting backdoors without anyone noticing.
Digital Pickpocketing (AC-2): Some routers simply scan for valuable data as it passes through, vacuuming up crypto wallet keys and cloud service credentials before anyone realizes they're gone.
What makes these attacks especially troubling is their stealth. Attackers can program routers to only strike under specific conditions—maybe after 50 normal requests, or when they spot the word "YOLO" in the data stream.
The Alarming Numbers
The research team put 428 routers to the test with disturbing results:
- 9 routers actively injected harmful code
- One attack emptied a test Ethereum wallet of $5 million
- Over 2.1 billion data tokens processed through vulnerable systems
- 401 AI agents were found operating with essentially no security checks
"These aren't hypothetical risks," Chaofan notes. "We're seeing real attacks happening right now, and most developers don't even know to look for them."
Why Nobody Saw This Coming
For years, AI security focused on protecting the brains (the models) and the tools—not the pathways connecting them. Relay stations became the overlooked weak link, especially as developers turned to cheaper routing options to cut costs.
"It's like installing a vault in your office but leaving the delivery entrance wide open," explains one cybersecurity expert reviewing the findings. "Attackers don't need to crack your security when they can just walk in with the mail."
Protecting Your AI Systems
For developers and businesses using AI agents, Chaofan's team recommends:
- Skip the middleman when possible—connect directly to official APIs
- Isolate and inspect any routers you must use, treating them like potential threats
- Encrypt everything—from requests to responses
- Watch for odd behavior like unexpected tool usage or strange API calls
"This isn't about abandoning relay stations," Chaofan clarifies. "It's about recognizing they need the same security scrutiny as every other part of our AI systems."
Key Points
- Third-party AI routers pose serious, often invisible security risks
- Attackers can manipulate AI decisions or steal sensitive data in transit
- Testing revealed millions in losses and widespread vulnerabilities
- Developers should prioritize direct connections and router security checks
- The industry needs new standards for relay station safety