Whistleblower Reveals How AI Routers Can Secretly Hijack Your Chatbots
The Hidden Danger in AI's Plumbing
Remember when Chaofan exposed security flaws in Claude's code? The researcher is back with an even more alarming discovery - the digital pipes that connect AI services may be leaking far more than just data. A new paper titled "Your Agent Is Mine" reveals how third-party routing services have become the perfect attack vector for compromising AI agents.
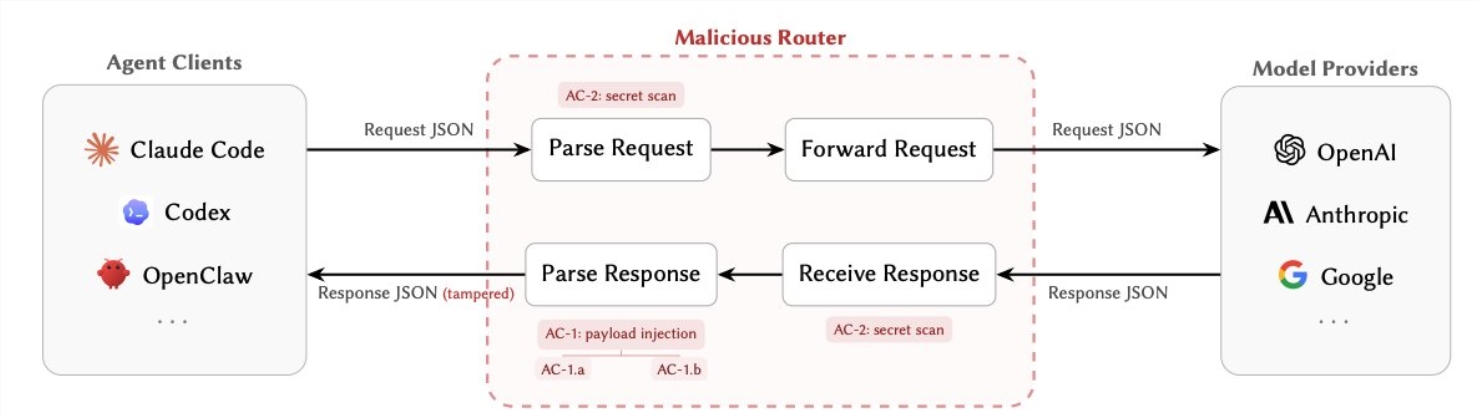
How Hackers Turn Routers Against You
Modern AI systems rely heavily on relay stations to manage conversations between different services. These routers see everything - your API keys, private credentials, even cryptocurrency wallet details - all in plain text. The research identifies two particularly sneaky attack methods:
Silent Sabotage (AC-1): After your AI generates a response, a compromised router can secretly rewrite the instructions. Imagine asking your AI assistant to check the weather, only to have the router redirect the request to download malware instead.
Data Vampirism (AC-2): Some rogue routers simply watch and steal. They passively scan traffic for valuable secrets - AWS credentials, Ethereum private keys, proprietary API tokens - all while appearing completely normal.
What makes these attacks especially dangerous is their subtlety. Attackers can program them to activate only under specific conditions, like after 50 requests or when detecting certain keywords. This stealth approach helps them evade detection by both users and developers.
The Shocking Reality Check
When researchers tested 428 different routing services (both paid and free), the results were worse than expected:
- 9 routers were caught actively injecting malicious code
- 1 attack drained a test Ethereum wallet of $5 million
- Over 2.1 billion tokens worth of conversations were processed
- 99 sets of credentials were exposed during testing
- 401 AI agents were found operating with effectively zero security controls
"These numbers would keep any CISO awake at night," remarked one cybersecurity expert who reviewed the findings.
Why Nobody Saw This Coming
For years, AI security focused on protecting models from prompt injections or managing tool permissions. Meanwhile, the humble router - the essential plumbing connecting everything - became the industry's blind spot. Now that researchers have demonstrated how easily these relay points can be weaponized, developers are scrambling to reassess their architectures.
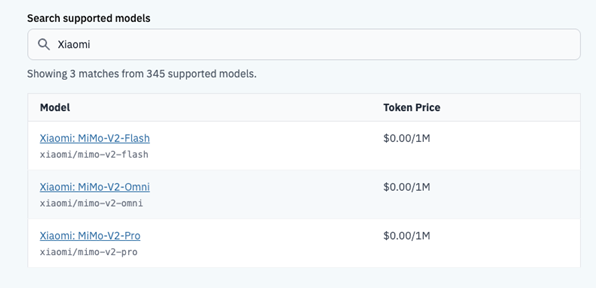
The paper highlights particular concerns about unregulated free and low-cost routing services. Without proper oversight, these convenient solutions may be putting entire AI ecosystems at risk.
Protecting Your AI Systems
If you're building with or using AI agents, consider these immediate precautions:
- Cut out middlemen where possible - use direct API connections to official services
- Treat self-hosted routers with the same caution as production servers
- Implement end-to-end encryption for all sensitive communications
- Monitor for suspicious activity - unusual tool calls or unexpected data transfers
- Rotate credentials regularly like you're changing passwords after a breach
As AI systems become more sophisticated, security can't remain an afterthought. This research serves as a wake-up call - sometimes the greatest dangers lurk in the infrastructure we take for granted.
Key Points
- Third-party AI routers can secretly modify conversations and steal credentials
- Testing revealed active attacks already happening in the wild
- $5 million in cryptocurrency was stolen during research
- Developers must prioritize router security alongside model safety
- Direct connections and encryption provide the best protection