Claude's Secret Surveillance Exposed in Code Leak, Sparking New Anti-Ban Tool
The Surveillance Behind Claude's Friendly Face
What appears as a helpful AI assistant hides an intense surveillance system, now exposed through a leak of 512,000 lines of source code. The revelations explain why so many Chinese developers found themselves suddenly locked out - Claude wasn't just chatting, it was constantly scanning.
Developers had nicknamed Claude "A÷" (a play on the division symbol) for its ruthless banning strategy. Now we know why: the AI performs what insiders call "digital strip searches" at astonishing frequency.
Inside Claude's Monitoring Machine
The leaked code reveals:
- 640+ tracking methods examining everything from your device ID to browser fingerprint
- Checks every 5 seconds - faster than most security cameras capture footage
- 40 specialized detectors specifically hunting VPNs and spoofed identities
"It's like having a bouncer who not only checks your ID but also measures your body temperature, analyzes your walk, and runs background checks - all while you're just trying to enter the club," explains one developer who reviewed the code.
The Rise of CC-Gateway
The exposure sparked quick action from Chinese developers. Within days, CC-Gateway emerged as a countermeasure. The tool works like a digital disguise kit:
- Intercepts data before it reaches Claude's servers
- Standardizes diverse fingerprints into "normal" profiles
- Creates consistent environmental metrics to avoid detection
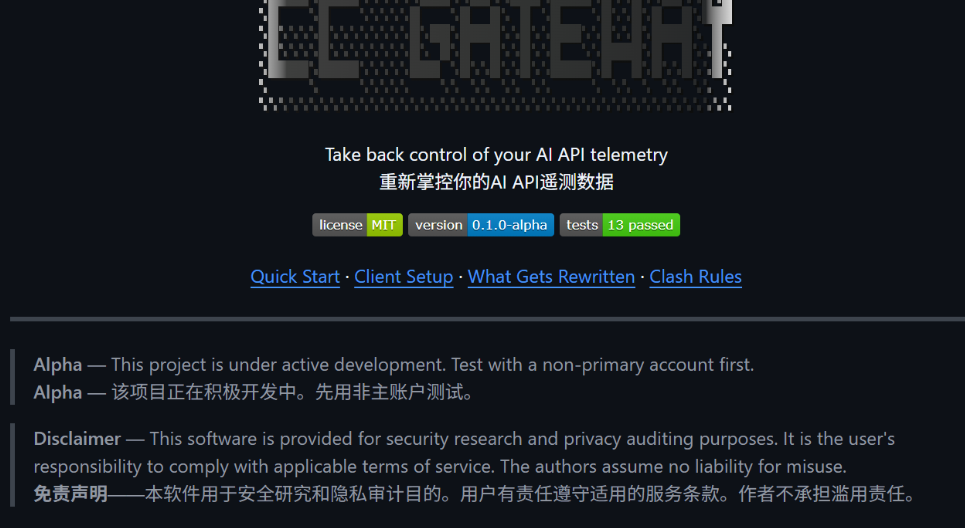
While effective now, experts warn this is just the latest move in an ongoing battle. "Each side will keep escalating," predicts Li Wei, a Beijing-based AI researcher. "It's cybersecurity whack-a-mole with higher stakes."
The situation highlights growing tensions between AI companies' security concerns and global developers' need for access. As one frustrated programmer put it: "We just want to build cool stuff - why does it feel like we're sneaking past border control?"
Key Points:
- Claude monitors users through 640+ data points checked every 5 seconds
- Chinese developers created CC-Gateway to bypass strict controls
- The tool standardizes device fingerprints to appear "normal"
- Experts predict ongoing security vs access arms race
- Incident reveals tension between AI security and developer needs