Researchers Uncover Critical Security Flaw in AI Relay Systems
AI Routing Systems Exposed as Security Weak Points
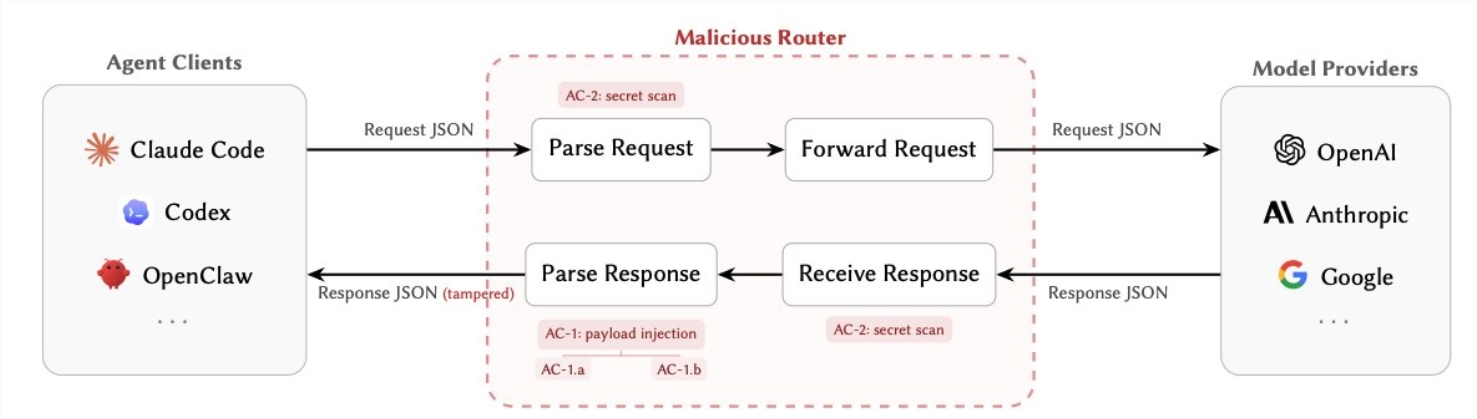
A team of cybersecurity researchers led by whistleblower Chaofan has uncovered a critical vulnerability affecting how AI agents communicate through third-party routing services. Their paper, "Your Agent Is Mine," reveals how these relay stations - commonly used to manage AI requests - have become prime targets for sophisticated attacks.
How the Exploit Works
Modern AI systems frequently rely on intermediary routers to process requests between users and language models. These routers, which handle messages in plaintext, can access sensitive data including:
- API keys
- Private credentials
- Tool call parameters
The research identifies two primary attack methods:
1. Payload Injection (AC-1) Attackers can modify tool call responses to redirect commands to malicious servers. This enables remote code execution, backdoor installation, and even long-term system infiltration through subtle URL manipulations.
2. Secret Theft (AC-2) Malicious routers can passively scan traffic for high-value information like cloud service credentials or cryptocurrency keys, all without triggering security alerts.
What makes these attacks particularly dangerous is their conditional activation - they might only trigger after certain thresholds (like 50 requests) or when specific keywords appear in the conversation.
Alarming Test Results
The team examined 428 routing services (28 paid, 400 free) with disturbing findings:
- 9 routers actively injected harmful code
- 1 attack drained an experimental Ethereum wallet of $5 million
- Over 2.1 billion tokens processed through vulnerable systems
- 401 agent sessions operated in completely compromised "YOLO" mode
The Industry's Blind Spot
"Router security has been the overlooked weak link in AI systems," explains the paper. While developers focused on model safety and prompt injection, few considered the risks introduced by these middleman services. The lack of regulation around free and low-cost relay stations compounds the problem.
Protecting Your Systems
For developers and enterprises using AI agents, the researchers recommend:
- Prioritizing direct API connections over third-party relays
- Implementing end-to-end encryption for all communications
- Regularly rotating API keys and monitoring for unusual activity
- Conducting thorough security audits of any self-hosted routing solutions
As AI systems become more integrated into business operations, understanding these vulnerabilities could mean the difference between secure automation and catastrophic breaches.
Key Points:
- Third-party AI routers pose serious security risks
- Attack methods allow both active interference and passive data theft
- Many existing relay services show signs of compromise
- Developers should review their routing solutions immediately

